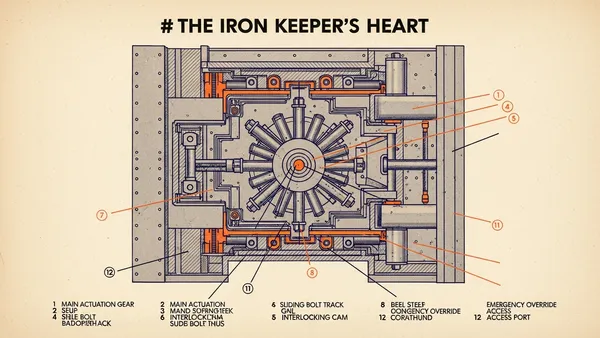
Stop Writing Authorization Middleware: Why Your Database Should Be the One Enforcing Your Permissions
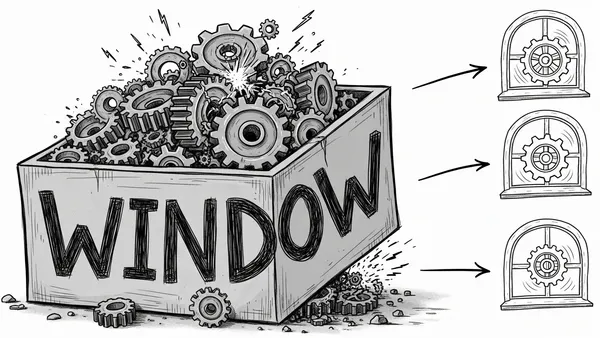
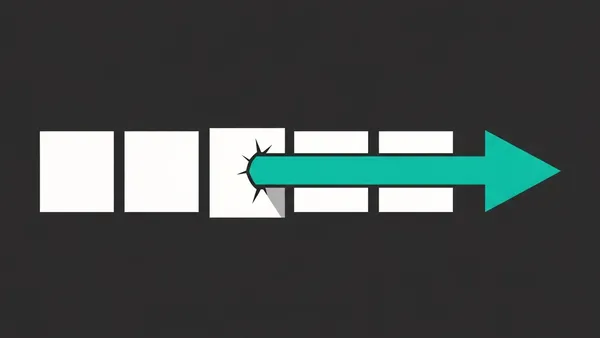
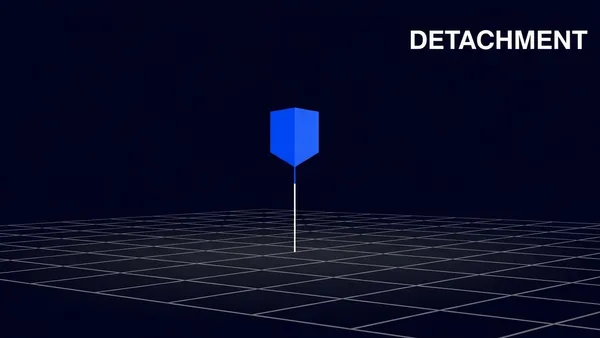
Shift your security perimeter from the application layer to the data layer to eliminate 'broken object level authorization' vulnerabilities once and for all using Row-Level Security.